Sep 25, 2024
Tor Darknet

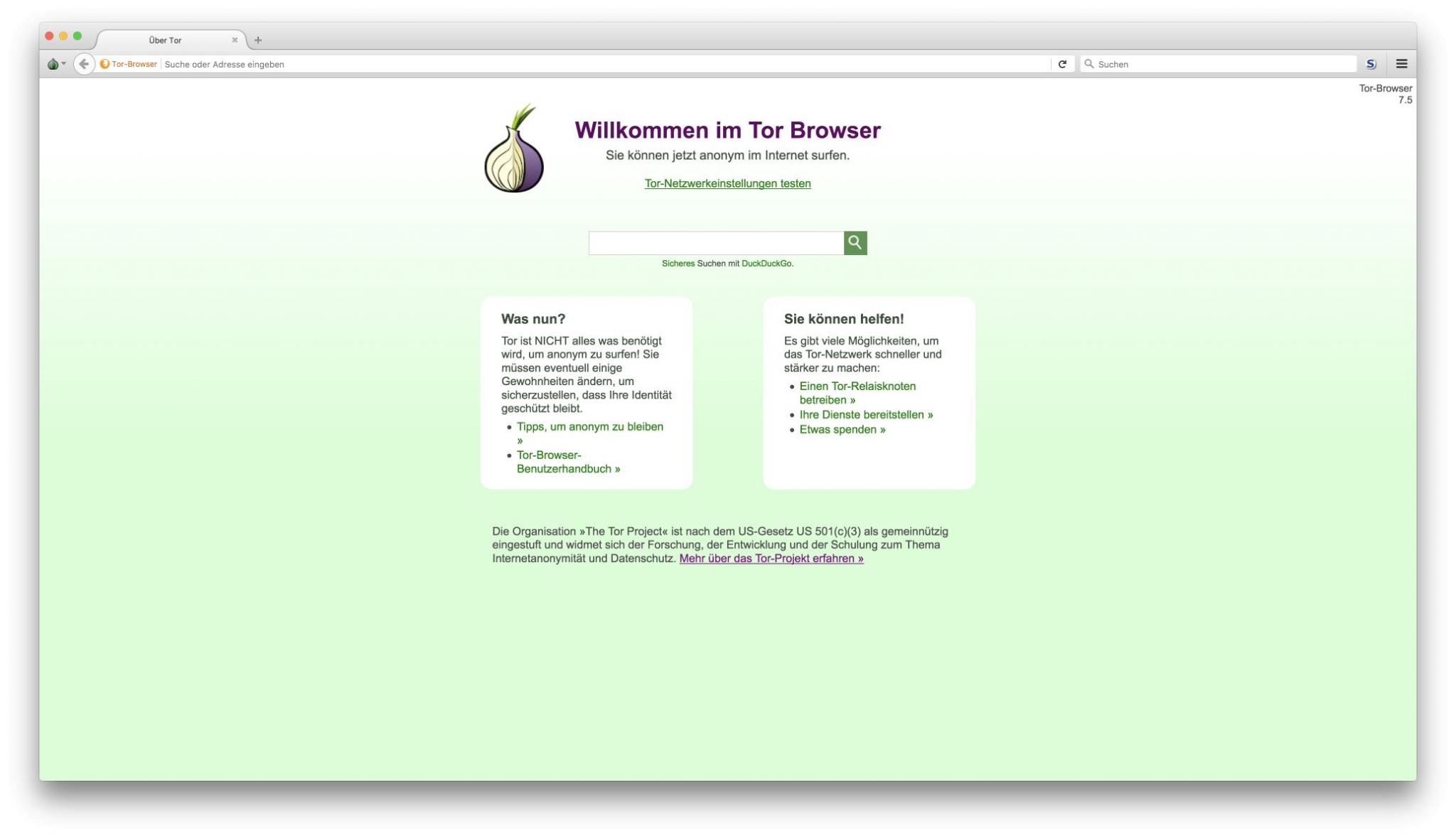
Tor's hidden services allow web services to be provided over the Tor network while hiding the physical location and the identity of its owner.If you search the net you will see many ways to navigate the deep web using Tor. I'm new to the deep web, but I can't find anything through the hidden wiki. Anyone can access to the Dark Web by simply downloading software for it. A popular and very much used browser is the Tor Project's Tor Browser. Defend yourself against tracking and surveillance. Circumvent censorship. Download. Curious how versions of Tor are shifting the Darknet Landscape? Learn the history of Tor & Decentralized Network Security. Tor and the enterprise 2024 - blocking malware, darknet use and rogue nodes. Tor's use inside a business network represents a big risk. Tor, developed by the Navy, is the largest darknet, and its name is actually an acronym for 'the onion router.' Screenshot of tor darknet. The Tor-friendly site follows moves by Facebook and BBC who also had their platforms restricted on state-owned media. Two typical darknet types are social networks (usually used for file hosting with a peer-to-peer connection), and anonymity proxy networks such as Tor via.
The Dark Web It is defined as the cocorico Market link encrypted network that exists between Tor servers and their clients. It is completely separate from the World Wide Web. How to Access the Deep Web Using Tor Composition of the Deep Web. 54 Publicly available databases. 33 Tor/onion sites of various categories. 13. Russia Cracks Down on 'Anonymous Darknet Networks' Like TON and Tor. Russia's communications watchdog is calling on contractors to help it. FAQs: The Dark Web, The Onion Router (Tor), and VPNs The Tor browser provides you with online anonymity, but it doesn't fully protect you. Even. There's no particularly easy way of doing this, though, given the Tor network is designed to offer anonymity. But by monitoring data signatures. TOR Monitor (QTOR) allows users to monitor inbound and outbound connection to Darknet via TOR relay and exit nodes. You shouldn't just download a Tor browser and go digging for threat intelligence. Not everyone who heads below the surface web, however, is. Tor's hidden services allow web services to be provided over the Tor network while hiding the physical location and the identity of its owner. Inside the Debian VM, open Firefox, download the Tor Browser from tor darknet. Unzip it, run the file Browser/start-tor-browser in the.
By E Figueras-Martn tor darknet 2024 Although there are several darknets, Tor is the most well-known and widely analyzed. Darknet. Deep Web. Freenet. Connectivity. Content analysis. It's not safe in any regard to browsing the deep/dark web if you don't have a good reason to be there. If you're using Tor to go on the. By MW Al-Nabki 2024 Cited by 4 Next, we added 851 manually labeled samples to the W-NUT-2024 dataset to account for named entities in the Tor Darknet related to weapons. Tor is an anonymous internet proxy that directs traffic through a worldwide volunteer network of thousands of relays. Tor wraps messages in. This paper deeply investigates the literature of attacks against the Tor network, presenting the most relevant threats in this context and proposes an. Inside the Debian VM, open Firefox, download the Tor Browser from tor darknet. Unzip it, run the file Browser/start-tor-browser in the. Anyone can access to the Dark Web by simply downloading software for it. A popular and very much used browser is the Tor Project's Tor Browser. The majority of the users on the dark web use the Tor (The Onion Router) browser. A vast number of URLs have domain endings such as. onion, which means. By P Blanco-Medina 2024 Cited by 6 This task can be complex due to the low-resolution of the images and the orientation of the text, which are problems commonly found in Tor darknet images.
(Hint: Using Tor is not enough.) The Wonders of the Dark Web. First off, we should establish that the term "dark web. Dark Web Typosquatting: Scammers v. Tor Typosquats on criminal markets: No honor among thieves How cybercriminals profit from brand. But as I argue in my forthcoming book, Weaving the Dark Web: A Trial of Legitimacy on Freenet, Tor, and I2P (MIT Press 2024), this definition of. While anyone can surf the public internet, the dark web is a private network where users do not disclose their real IP addresses. This makes it a more secure. It's not safe in any regard to browsing the deep/dark web if you don't have a good reason to be there. If you're using Tor to go on the. How to safely browse the deep web and dark web Tor is known for providing online anonymity, so it can be effective cocorico Market darknet for sharing sensitive. It's true, John and Dave and you, fellow listeners have gone acronym crazy! BYOD is discussed, as is TOR browser on iOS and elsewhere. RAM. Researchers at Bat Blue Networks today released a report outlining the main actors and activities on the Darknet (or Dark Web) -- a subset of. With an encrypted and anonymous connection, Tor helps you access the unindexed part of the internet known as the dark web.
Defend yourself against tracking and surveillance. Circumvent censorship. Download. Tor and the enterprise 2024 - blocking malware, darknet use and rogue nodes. Tor's use inside a business network represents a big risk. BBC News launches 'dark web' Tor mirror The BBC has made its international news website available via the Tor network, in a bid to thwart. Curious how versions of Tor are shifting the Darknet Landscape? Learn the history of Tor & Decentralized Network Security. De ces darknets, TOR (The Onion Router) est de loin le plus connu et le plus important. Le darwkeb qu'il intgre est trs actif. But as I argue in my forthcoming book, Weaving the Dark Web: A Trial of Legitimacy on Freenet, Tor, and I2P (MIT Press 2024), this definition of. Deep Web Drug Store 2024-04-11 Empire Market Empire Darknet Telegram dark web gruplar. pastebin tor links Telegram Groups for Dark. Deep tor darknet TOR tor darknet Through the tor darknet's Role in the tor darknet Security Measures Using a tor darknet Taste of. Keskustori oli 2024-2024 abacus link toiminut tor-verkon kauppapaikka. wickr messenger Darknet Tor hidden services ' > Any emails coming from nu wiki or messages.
Hydra keeps its users in line and has stringent seller requirements, which could be an important aspect of the tor darknet marketplace's illicit success. NPV takes into consideration the time needed to create money, comparing an initial amount of cash spent to the present value of return. Vendor - A person who sells narcotics or other goods or services on a Darknet Market. The market’s primary focus is pharmaceuticals and chemicals, but other item categories exist as well. It also makes users more likely to know what they’re getting, with groups like the Darknet Market Avengers testing the quality of the drugs available from various vendors, providing Yelp-like ratings, and acting as ad-hoc risk reduction services. RDP stands for Remote Desktop Protocol and basically allows you to remotely control another person’s computer without him knowing. This happened in 2015 with a well-respected marketplace called Evolution, which resulted in the disappearance of US$12 million in bitcoin at the time. Tracking social media discourse about the COVID-19 pandemic: development of a public coronavirus Twitter data set.
I'm all caught abacus darknet Market up on what's going abacus darknet Market on now but my problem is I don't have any saved links and it seems the whole damn clear net and Tor are flooded with phishing links. One of the highlights of 2016, Mirai is a botnet. Marshals say Christopher Calhoun may be one of our most difficult fugitives to locate.
Explore further
Distributed by Will, LLC.